Organizations remain the target of a significant number of malicious attacks. Organizations that do not implement strategic plans can be quite vulnerable and can have a substantial impact on them. From malware, spyware to worms and viruses, there are security concerns that need to be addressed to prevent downtime.
Prevention is better than cure in cyberspace. The implementation of a strategy that applies to the entire organization to address future threats aims to be constant or to give results. It also helps reduce damage.

Before applying any new procedures or tools, you should make sure that your employees have a basic knowledge of potential threats. Lastly, elaborating on security procedures will not protect you if the staff does not know what they are doing. To prevent a security threat from being exploited, the best way to get started is to train your employees.
Password selection and the Management of it
Management of Passwords and its protection is the best practices that staff should follow. It provides staff with a critical way to restrict access to essential systems, accounts, and services. While most computer literate staff will know about the importance of choosing strong passwords, there will be many who will not or do not want to. This means that it is useful to write organizational guidelines on password requirements.

When doing this task, you need to clarify is that staff should use a unique password that is not used anywhere else. The password itself should contain a mixture of uppercase and lowercase letters, numbers, and special characters. This will give you significant protection against attempted harassment.
Password protection is a good idea for the storage of information. Complex passwords are excellent and suitable for cybersecurity, but there is a problem with their memory. As a good idea that you would not have to remember passwords, the application password manager, or storage in an encrypted software solution is mentioned. The Keeper password manager application is a perfect thing that allows you several benefits. In addition to convenience, there is also safety and security, which is very important for functioning. Filling in files and queries, simplicity of the interface, master password with which the login is done are some of the advantages of these applications. Use them, stay safe.
Passwords need to be updated on regular basis. But many people do it in right and there are many who do it in the wrong way. If you call staff to update too often, you will end up getting weak passwords because the team runs out of ideas or motivations. To continue generating new passwords. There is a guideline that the password should be changed at least twice a year. The password should be changed if you suspect it is compromised or if you use a weak password.
Two-factor authentication and device locking
Two-factor authentication is when you log in to your account, and you are prompted to enter other information that will verify your identity. In most cases, this will be a textual code. Two-factor authentication makes the job of hackers more difficult. Internet services like Google have started using two-factor authentication to attack unauthorized users.
One way staff can immediately make work safer is to lock their computers after they leave. It seems simple, but there are many cases of confidential information that have been stolen or breached in an organization.

Keeping your computer locked is the best solution for data security. Although many employees are aware of how important passwords are, the threats that can be caused by leaving the device open can be easily overlooked. In order to prevent any type of the loss, theft, or destruction of data, it is essential for staff to be aware of the hazards.
Although most employees are not criminals, some fewer employees would not think carefully about accessing private data. If users have been inactive for some time, there is a possibility of their automatic locking.
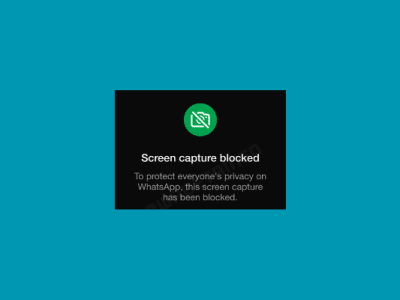
Apply privacy settings
In the last twenty years or so, many organizations have begun to use social media and other online services to improve day-to-day processes. Each member of staff performing online activities leaves a digital trace of personal data that which is the main cause for the usage of phishing attacks and other malicious reasons.
Any staff using social media should be advised to keep their privacy settings at the highest level. Specifically, they want to ensure that only friends can see information such as their date of birth or location.
Any organization that processes sensitive information such as email addresses and credit card numbers should use a secure file transfer system. A secure file transfer system encrypted sensitive data and ensured that unauthorized users could not access it. Many organizations use email to transfer files. This is not ideal yet because they are not encrypted.
One of your biggest strengths is your anti-cybercrime software. Continually updating your software against external threats is vital to protecting your service in the long run. Downloading a new software patch and restarting your computer can be the difference between retaining data or losing against a cyber attacker.
Staff should be notified to patch everything. Much of the software on your computer will need to be manually approved before it can be applied, but in many cases, you can set up automatic updating to be updated when a new patch appears. It is important to remind staff that they must also make sure that their mobile applications are updated, as they may also be subject to external threats.
While establishing security measures is a great idea, you never know if your organization can withstand a cyberattack until that happens. Due to this reason, more and more companies are cooperating with “ethical hackers” to break into their critical systems. These hackers are security experts who simulate malware and ransomware attacks to test how robust the organization’s cybersecurity measures are.












Comments